Many Wi-Fi network administrators decide to disable SSID broadcasts. They do this, in part, in an attempt to hide their network from uninvited users. The common belief behind it is that if the network name is not being broadcast, it is harder for an attacker to find the network.
Nothing could be farther from the truth. Finding the name for a non-broadcasting Wi-Fi network is, with one exception, almost as easy as finding the name for any other Wi-Fi network. I’m demonstrating one easy method to do it here.
Using Kali Linux to Find Hidden Wi-Fi Networks
I’ll use Kali Linux for this example. Kali is currently the single best penetration testing and security tool available, as it contains most every tool I could want in a minimalist operating system. I’m running Kali Linux with Debian kernel 3.18.0 on a Lenovo X230 laptop. I’m also using the built-in Intel wireless NIC, so I don’t need any third-party or custom hardware. This is the network hardware showing the Intel WNIC assigned to WLAN0 and not associated with an access point:
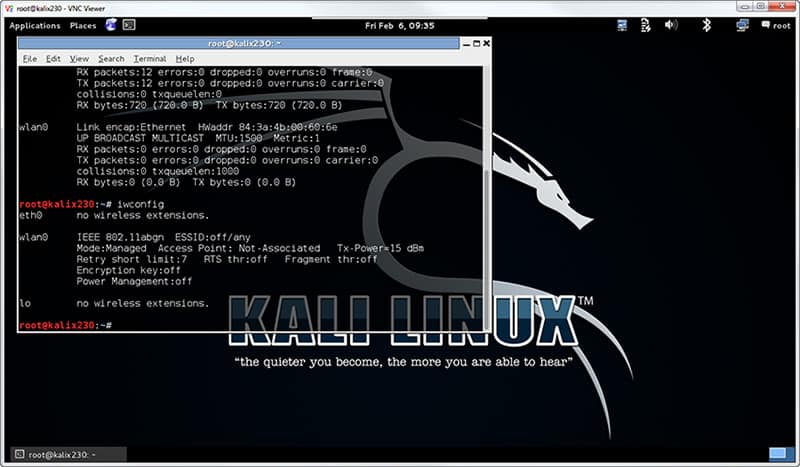
Figure 1. The Intel WNIC is waiting to do my bidding.
I only need to execute two commands. The first one is airmon-ng start wlan0:
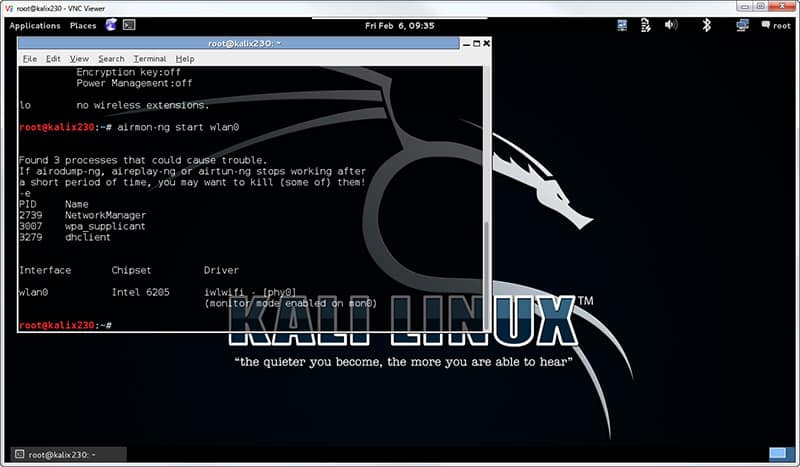
Figure 2. The Intel WNIC is ready to rumble!
I can safely ignore the warning about process interference for this example. If I wanted wireless networking to work consistently, I might have to kill those processes. But they usually don’t interfere with scanning for hidden networks. The result of this command is that I have a new interface, mon0, assigned as a monitor mode port for wlan0 (the WNIC).
Before the next step I usually scan to determine the Wi-Fi channel my target is using. This is a purely optional step, as I can scan all channels until I succeed. Identifying the channel can be done with a variety of tools, including the tool I use next, and will be the topic of a future blog. For this example, my target access point is on channel 11 (2.462 GHz).
Now I fire off the process by executing airodump-ng –c 11 mon0 as shown:
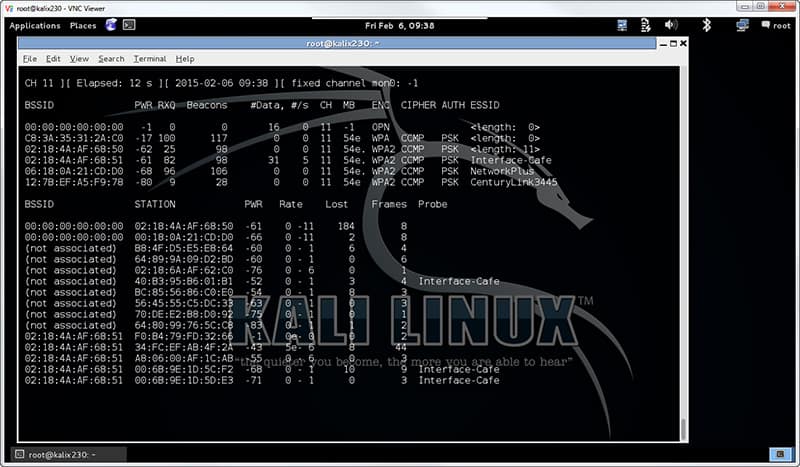
Figure 3. Invisible airwaves crackle with life.
I can already see several wireless network names in the ESSID column. The target network is there as well. But since the name is currently hidden, it appears as <length: 0>. I know it’s the target based on the BSSID, or MAC address, matching my reconnaissance data. I see more than one <length: 0> entry, and each of those represent a separate Wi-Fi network that is not broadcasting its name.
Now I need to wait. Whenever a client connects or reconnects to this network, the access point sends its ESSID in the clear as part of the wireless association handshake. Sure, I could force clients to disconnect and reconnect through a denial of service attack, but that’s more aggressive than I want to be for this penetration test. As long as one client is connected, the reconnection will eventually occur. And the more clients that are connected, the less time I need to passively wait before…
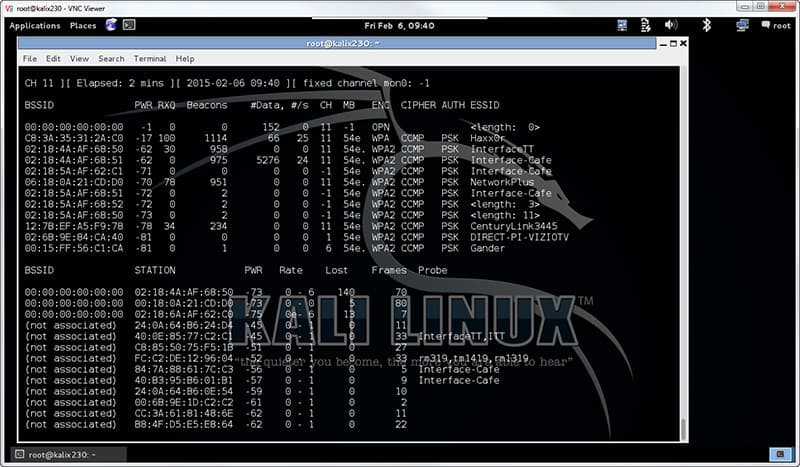
Figure 4. Drop the mic, I’m done.
Note that airodump-ng has been running for 2 minutes as shown at the top left of the window. I see several more networks, some of which were previously hidden. My example SSID is Haxx0r, shown as the second one on the list. Of additional interest is the fact that I don’t see the names of the networks that have both minimal traffic and hidden names. That’s the primary flaw in this technique – if there are no clients an no traffic on the wireless network, getting the name will prove difficult. Luckily, that doesn’t come up very often.
Enjoy!
enoK -CISSP / MCSE / PMP